|
Hi CuddleChunks! Thanks for starting this! I also work at an ISP and we've been using them a lot. Mostly for endpoints of a point to point connection or when a customer needs a VPN and such. They're much much cheaper and nicer than ASAs. As far as reliability... we don't have many in the field for an extensive amount of time so it is hard to tell. They're pretty nice though. As far as pfsense -- on x86 hardware pfsense will probably kill this in terms of routing capabilities if you're using a good NIC. My #1 gripe about Mikrotiks is that it's based on Linux. If they put in a bit more time and developed on FreeBSD they'd have a much more solid product with a better network stack and access to OpenBGPD which is MUCH better than the BGP software used here. tl;dr I think you're crazy if you're replacing the core infrastructure of your ISP with Mikrotiks. However, it works great for vpns, firewalls, and endpoints.
|
|
|
|

|
| # ¿ Apr 28, 2024 17:54 |
|
I have to do some VPNs between Mikrotiks and ASAs soon. We don't have this specific setup in production anywhere yet as we usually do between Mikrotiks. Anyone know if there are any pitfalls I should beware?
|
|
|
|
Hi guys, I need some VRRP help badly  The issue is this: I have two VRRP instances running on each RB1100. One is VRRP-External and the other is VRRP-Internal The problem is that only whole device failover works. If the one that is MASTER for both is running and you unplug the internal interface only the internal interface fails over to the secondary router. This is not good. Effectively what happens is the traffic keeps flowing to a router but now it has no way to get out because it is not master of the VRRP-External. I'm sorely disappointed because I've been spoiled by BSD's CARP which automatically fails everything over if you enable preempt -- this is an extra feature they added apparently. I assume this could be figured out with some script? So far I'm not having any luck figuring out what I need to do it. I've located some scripts but even when I tell them to run the run count doesn't go up... I'm referring to this thread: http://forum.mikrotik.com/viewtopic.php?f=9&t=42545 Thanks to anyone who can help!
|
|
|
|
adorai posted:In vyatta you would use a vrrp sync group. Not sure if mikrotik has something similar, but since they are both based on linux I am guessing it does. Negative, it does not have this feature. Sounds like Vyatta did VRRP the right way... karoshi posted:You ain't running no dynamic routing protocol (which should detect the removed cable and announce the lack of connectivity upstream to the external ~cloud~). Even running a dynamic routing protocol on the network would not solve it. I don't think you're considering that I'm using VRRP and no routing protocol can detect that a cable has been removed because of how VRRP works.... karoshi posted:Static route solution: Add a cable between the 2 routers, add a static route with less precedence to the other router. Repeat for the external interfaces' routes. I was actually discussing this with a coworker last night and the only good solution we could come up with is to run a cable between both Mikrotiks and run OSPF. * Cable gets unplugged * Traffic routes to other Mikrotik which is in Backup mode for the uplink side * OSPF routes traffic over to the other Mikrotik which has Master * Off to the internet it goes! This should work fine as long as VRRP plays nice and when you're the Backup it doesn't have the uplink's entries in the routing table. We have yet to test that, though. feld fucked around with this message at 17:43 on Feb 17, 2011 |
|
|
|
karoshi posted:For the other side I'll assume a default route. Add a static route on R-A pointing to R-B with a "distance" higher than 1 (the default distance for static routes) and vice versa. Again, you got yourself a nice routing loop if both upstreams are cut. I certainly know how OSPF, etc works, so I know what you're talking about. However, we implemented the Mikrotiks for the customer tonight and all but one failover scenario worked correctly. (Mind you, we have IPSec VPNs and whatnot also involved which makes this setup pretty rad because the IPSec failover is nearly instantaneous in our testing) OK, so current failing "failover" scenario: * Router A is master * Connections to LAN on are cut on Router A * Router B picks up as master for LAN's gateway * Router B has an extra link going back to Router A with OSPF going over it and all the VPNs * You can still contact all INTERNAL networks (local and over VPNs) that were advertised by OSPF. However, you can't access the internet because Router B isn't the master of the uplink so its default route is failing Thoughts? How can I get OSPF to tell the other router that it has access to the internet and inject a default route into its table telling it to go over the link between the routers? I'm very tired right now and haven't put a lot of thought into this scenario, but outside of scripting or possibly trying to add a second default route with a higher distance... I'm stumped  We have equipment to test this tomorrow so hopefully we can come up with a solid and reliable solution.
|
|
|
|
Turns out it just won't work with the Mikrotik VRRP solution. Full failover or bust. The way the VRRP works on there it will cause conflicts because both think they own the addresses when the link is cut. Note, this might not be the same conclusion for people who aren't doing a bridged interface for two links to from each Mikrotik to two switches as the interface would actually go down. Bridged interfaces don't really go down.
|
|
|
|
NOTinuyasha posted:The OP of the MikroTik thread, scared of a little QoS? QoS is the main thing that I hate about Mikrotiks. I can deal with the fact that setting up firewall rules is a bit more cumbersome than it needs to be. However, the QoS is atrocious -- they just tacked a GUI on the already terrible Linux QoS. I'm planning on selling mine for some pfsense compatible gear -- pf is a better firewall and does better QoS anyway.  Mikrotik can't match empty ACK packets which kills its QoS potential. http://www.benzedrine.cx/ackpri.html
|
|
|
|
insularis posted:Thanks, Weird Uncle Dave. I'm feeling confused over the Virtual AP stuff in RouterOS. I understand your technique, but I'm unsure of how to go about that with pfSense as the bridge and sole DHCP server (trying to avoid double-NAT). I don't have any idea how to get pfSense to serve out a particular range for one of Mikrotik's SSIDs and another for the Virtual AP SSID. Multiple bridges which bridge a vlan and the virtual AP. Routing does the rest. You serve the DHCP on separate VLANs.
|
|
|
|
leave eth1 as-is setup a bridge. add the rest of the eth ports and the wlan to the bridge set the dhcp server to serve IPs on the bridge interface it will now do what you expect.
|
|
|
|
Does this help?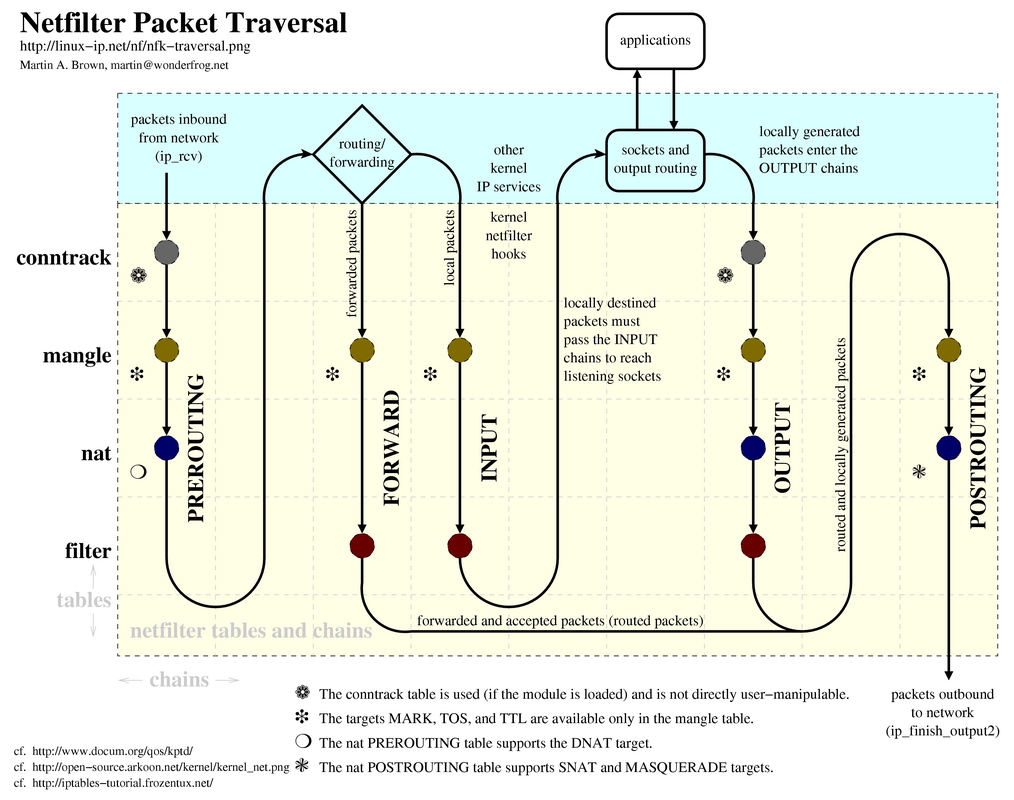
|
|
|
|
R1CH posted:Anyone else having problems with the DNS server on MT units? It seems any DNS with low TTLs seems to randomly not resolve, it's super annoying. This most often happens with Amazon S3 and thus affects all kinds of websites. Happens across the LAN so it's not related to a single PC, it seems to return a NXDOMAIN (instead of a SERVFAIL) which my Windows PC happily caches until I flushdns, at which point it usually starts working again. YES YES YES YES YES 100% exactly -- Amazon and all And now that I know someone else has experienced this we can properly blame the Mikrotik and work around it on a future re-deployment at this customers location. Thank you!
|
|
|
|
Ninja Rope posted:Not that this is specific to MikroTik (it's 100% true with Cisco and everyone else too), but just because a device has gigabit ethernet ports doesn't mean it can handle that fast of an internet connection. Depending on the configuration it can switch internal traffic at 1gbps in each direction per port, but only relatively expensive gear can handle a gigabit internet connection (routing, NAT, ACLs, etc) at full speed. Even the cheapest gig switches these days should be able to do 1+Gbit/s on its switching fabric. *Routing* gigabit is a different monster though.
|
|
|
|
NOTinuyasha posted:The RB751G is now available - same as the RB751U, but with gigabit ethernet. STOP TELLING PEOPLE I WANT TO GET MY ORDER IN FIRST
|
|
|
|
CuddleChunks posted:QoS is loving voodoo but there are online guides about it. My biggest annoyance is QoS on anything Linux-based. I wish Mikrotik would just rip all that out and replace it with something nicer.
|
|
|
|
Farking Bastage posted:That coupled with tarpitting does extremely unkind things to the tcp stack of anyone who tries to portscan me. The tarpit feature just has you hold connections open and slowly respond. You're really doing more harm to yourself. Sure, if some kid get your IP and portscans you they're kind of hosed, but anyone launching a real DDoS attack (scanning first, we'll say)? YOUR network stack will melt because you'll exceed 65535 open ports in no time.
|
|
|
|
Farking Bastage posted:e2: Maybe I misunderstood tarpit. I thought it basically sent back ack flags regardless of whether a port is open or not causing an attacker's TCP stack to poo poo itself. I can't comment further as my quick googling of what tarpitting was on mikrotiks seemed to describe what I was talking about. It sort of aligns with your description as well -- you're causing their scan to go slow by responding on all ports. But again, it could backfire.
|
|
|
|
Ninja Rope posted:Not to rain on your parade, but no good scanners use the host's IP stack to do scans, it's all done in userland, So the entire concept of making a tcp or udp connection to another host is done in userland? The utility runs in userland, sure, but the kernel still has to open a socket. Any network activity at all has to go through the kernel and network stack at some point or it simply will never reach your NIC and hit the wire. TCP connections don't die immediately when you're done unless they're closed cleanly (unlike tarpitting). They're held open for quite some time by default on nearly all platforms -- "CLOSE_WAIT". This is what kills you. You'll run out in no time. And we're not even taking into consideration the limitations of session tracking on different platforms' firewalls. edit: and really, this is only a serious issue in certain situations. On your home connection? You're probably fine. But if I was an intelligent-but-angry teenage angsty nerd who wanted to show you up I'd start by scanning before I launch an attack. And when I realize you're tarpitting me? Time to push out a script to 20 different hosts to each open defined port ranges to your router every X minutes. Doesn't take much traffic and now you're dead in the water. feld fucked around with this message at 06:50 on Feb 10, 2012 |
|
|
|
Ninja Rope posted:You're also confusing the number of unique TCP and UDP port numbers (65535) with the number of active/outstanding connections. A host can have more than 65k open TCP connections if it has the memory. I think we're simply misunderstanding each other here. I certainly understand the concept of more than 65K open TCP connections. Like if you have a webserver and you have 100,000 clients hitting it at once. That's fine, assuming your webserver can handle it. It's your port 80 to 100,000 other ports, one on each of the clients. But if this tarpitting pretends that every port of yours is open to slow a scanner down... Now you can easily have your ports 1-65535 being used up very quickly. You can't make further outgoing connections because there's none left in the pool. You're now dead in the water because all of your ports are exhausted. See what I mean?
|
|
|
|
Ninja Rope posted:That's true, if some hypothetical tarpit program created and bound one socket per unused ephemeral port the host would be unable to initiate any outgoing TCP connections. However, that would be the case as soon as the sockets were bound, not triggered when someone connected all of the ports. The Linux/iptables tarpitting implementation is done inside iptables and doesn't prevent the port from being used for other connections. I don't know how the Mikrotik tarpit implementation works, but I imagine it uses iptables. I'm still a little fuzzy about how the firewall would respond on a port but the OS has nothing bound to it. Either way, I completely ignored the fact that yes, something would have to be bound to EVERY port. You've made an irrefutable point. Thanks for following up. 
|
|
|
|
Ninja Rope posted:I hope I didn't come off as if I was trying to bust your balls, I've been working on something related for a while and felt like sperging out. Sorry if I seemed like a dick. Nope, no worries. And thanks for the link -- I'll browse the source later. Cheers!
|
|
|
|
I can't wait until 2015 when we finally see a RB751G! Mikrotik needs to find some friends in the FCC because this is just getting ridiculous.
|
|
|
|
You should have put the external antenna on the 751. In my (not so scientific) tests it's improved the signal by 10db.Nystral posted:Does anyone have a number I can use to contact Roc-noc? they haven't responded to my query via the form yet. I don't know if Tom's number is actually on the site but he's answered his personal cell phone for me in the middle of his lunch to listen to some pretty inane questions. feld fucked around with this message at 14:02 on Jul 13, 2012 |
|
|
|
arnika road posted:The only complaint I have is that with the license level the RB2011 comes with, you can't do RADIUS accounting for this many people (it stops working at 20 active sessions). Authentication only. Can't you pay out of pocket for a license upgrade? I thought at one point this was possible on certain hardware. It's not like $100 or whatever is going to kill you when you're talking about a $3,000 sonicwall 
|
|
|
|
NOTinuyasha posted:You can sign up for Hurricane Electric's IPv6 tunnel service and push all DNS requests over that? That seems like a sane response to me. It's free and they probably have a tunnel server local enough that there's no impact on performance. I wouldn't trust that every application can handle doing IPv4 lookups to an IPv6 DNS server. There's still a huge amount of broken DNS stuff out there and remember not every program uses the OS DNS recursor code. First example off the top of my head is FireFox. edit: Chrome also has their own DNS recursor code. feld fucked around with this message at 17:46 on Aug 20, 2012 |
|
|
|
movax posted:Basically: 1. vlan at the switch port, not at the computer/device's NIC. (this is untagged traffic, vs making the device tag the traffic which support might be inconsistent) 2. certainly as long as your firewall knows how to talk to that VLAN too 3. yes, that host would have to have a trunked port and have virtual NICs each tagging traffic for each network VLAN's aren't quite that complicated once you set it up, but sometimes they're hard to explain
|
|
|
|
Has anyone seen an RB493 just suddenly begin failing to get DHCP from a cable modem? Had a customer call up with that and it was quite bizarre. Still think it's his ISP as it gets a link and everything. He can also plug in *any* other device and get his IP. In other news, I have an RB750G that needs a new home. I have too many network devices. PM me if you're interested.
|
|
|
|
PUBLIC TOILET posted:Before I bitch to Time Warner again, has anyone heard of common issues with regards to a MikroTik router randomly experiencing packet loss? Just started this past week and I've had to call Time Warner support once already. Connection was experiencing 25-50% packet loss according to the RouterOS ping tool then the whole connection went dead. Overseas support did something to the cable modem that brought it back to normal. Now I'm experiencing the problem again only this time RouterOS is telling me it's around 15-25% packet loss. I'm quick to blame Time Warner for the issue but I just want to make sure there aren't any known random packet loss issues related to the MikroTik equipment. Yes, and it's the main reason both myself and a coworker ditched our RB75(0|1)?g as home routers.
|
|
|
|
SopWATh posted:What did you switch to? Is the alternative any better? Juniper J2320 / SRX210. Juniper's awesome, but it's far from cheap. The stability is worth the money for me.
|
|
|
|
CuddleChunks posted:Hahah holy poo poo. Moving from a $70 router to a $2000 dollar unit should do the trick. You can find J2320s on eBay for ~200. I didn't buy mine "new".
|
|
|
|

|
| # ¿ Apr 28, 2024 17:54 |
|
writing test suites is hard
|
|
|






