|
CLAM DOWN posted:Being "passionate" about something does not equate whatsoever to not having work/life balance, working 60+ hours/week, being "emotionally invested" in a company, etc. You're right in that it doesn't HAVE to, but by and large everyone I've known who I'd consider "passionate" about their work rather than just "proficient" (even extremely proficient) are exactly the types who end up dicking up their work/life balance, getting emotionally invested in stuff, etc., precicely because they ARE passionate about it.
|
|
|
|

|
| # ? Apr 19, 2024 03:30 |
|
yep. i mean, if "passionate" just means "enjoys their job/the field" or "finds infosec interesting" then ok whatever. but the original question was if you have to be "passionate" due to low pay, which is much more in line with the word as i'm using it like, it seems to me that "i am passionate about hacker poo poo, and don't do it outside of work" has some tension in there, and i think most folks would agree. maybe it shouldn't be that way, but meaning is use etc etc Achmed Jones fucked around with this message at 17:12 on Feb 20, 2021 |
|
|
|
Passionate can mean that at a minimum you�re not just a mercenary in it for the money and you have a greater personal interest in the field or work. I�d agree that generally �find a job you�re passionate about� has often been horrible advice and puts people on an impossible quest for imaginary fulfillment. Being more generally passionate about self development and always trying to do great work, regardless of your actual job, is more useful than just being a huge fan of something narrow and specific.
|
|
|
|
I do a lot of related work to my job as a personal hobby outside of it, which makes me a better employee. I don't work on my employer's projects in my off time, but I do work on and look at things for fun that improve my skills and knowledge... like this thread.
|
|
|
|
interest in subject matter is a sliding scale I don't know why otherwise-professional people get so weird about this poo poo, especially in interviews
|
|
|
|
when i hear passionate, i think about rogue brewery
|
|
|
|
Jeoh posted:when i hear passionate, i think about rogue brewery That job listing actually made me less passionate about my job
|
|
|
|
DrDork posted:You're right in that it doesn't HAVE to, but by and large everyone I've known who I'd consider "passionate" about their work rather than just "proficient" (even extremely proficient) are exactly the types who end up dicking up their work/life balance, getting emotionally invested in stuff, etc., precicely because they ARE passionate about it. I consider myself "passionate" about security by the objective definition of the word. I love security, find it fascinating, and sometimes mess around with it for fun outside of work. I also work 36.25 hours a week and not a minute more. Time at/invested in work and passion/interest are mutually exclusive concepts.
|
|
|
|
CLAM DOWN posted:Time at/invested in work and passion/interest are mutually exclusive concepts. I assume you mean orthogonal rather than ME, unless you're claiming you can't do both
|
|
|
|
Potato Salad posted:interest in subject matter is a sliding scale "Passionate" workers train on their own time instead of on the company dime.
|
|
|
|
CLAM DOWN posted:I consider myself "passionate" about security by the objective definition of the word. I love security, find it fascinating, and sometimes mess around with it for fun outside of work. I also work 36.25 hours a week and not a minute more. Time at/invested in work and passion/interest are mutually exclusive concepts. ding ding ding Except for the last line. But right on otherwise.
|
|
|
|
Rufus Ping posted:I assume you mean orthogonal rather than ME, unless you're claiming you can't do both Correct, sorry.
|
|
|
|
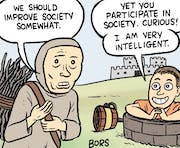
I love the future of sudo aliases https://twitter.com/CubicleApril/status/1363918513665175552?s=20
|
|
|
CommieGIR posted:I love the future of sudo aliases
|
|
|
|
|
CLAM DOWN posted:Being "passionate" about something does not equate whatsoever to not having work/life balance, working 60+ hours/week, being "emotionally invested" in a company, etc. Some of you are taking making huge extrapolations and leaps here and clearly have wild definitions of "passionate".
|
|
|
|
hi infosec ppl recently i started working for a security saas product/company. over the course of the last few months i've had dozens and dozens of conversations with CISOs at organizations of all different sizes holy poo poo they are all totally useless. they don't have the authority to buy anything, they inevitably wind up begging the CTO or CFO for special budget exceptions. they don't have the skills to do/install/deploy anything, they inevitably wind up begging the CTO/DevOps ppl to actually set stuff up for them. they don't have the access to fix anything, again they're just filing JIRA tickets and begging people to listen to them. as far as I can tell they seem to have about as much budget and authority as a mall cop. anyway thats it, no question here, just figured i'd commiserate with people who probably already know this from the other side.
|
|
|
|
MightyBigMinus posted:they don't have the access to fix anything, again they're just filing JIRA tickets and begging people to listen to them.
|
|
|
|
Im only like 3 months into my InfoSec job coming over from a full time network engineer role. I work way less hard than I use to. My job seems to involve talking other teams into fixing their poo poo, then escalating to management as the fixes go unimplemented, before moving onto the next broken thing. Its not nearly as fun as my old job but it pays a ton more at least.
|
|
|
BaseballPCHiker posted:Im only like 3 months into my InfoSec job coming over from a full time network engineer role. Infosec is mostly delegating I've found. I don't know Ruby so I punt all fixes to devs.
|
|
|
|
|
CyberPingu posted:Infosec is mostly delegating I've found. True in my experience as well. Most places big enough to have a full time security staff are also big enough to be bogged down by necessary bureaucracy and management making changes slow and tedious enough as it is.
|
|
|
|
BaseballPCHiker posted:Im only like 3 months into my InfoSec job coming over from a full time network engineer role. Pretty much, kinda want to go back to consulting since doing IR/DR and Pentesting was a lot more fun, but a lot less stable pay wise/job wise.
|
|
|
|
Our CISO isn't even an employee; theyre a consultant that our Exec IT director calls vCISO and he's even more useless. But he tells the board we have done xyz (i did xyz) and collects 250 an hour.
|
|
|
|
MightyBigMinus posted:hi infosec ppl This is so relatable it hurts. I used to work in R&D/detection development for a SIEM product and honestly can't say that it seemed like there was any net gain made in terms of customer security. It was primarily purchased by CISOs who were the only security staff at the company, usually outsourced triage/IR to a SOC, and whose entire understanding of security was that the magical box would prevent any and all issues. It got worse when everyone started demanding investment in cloud products and detections, because those detections are even noisier than info-level portscan garbage if they don't have solid cloud architecture practices to begin with (they didn't).
|
|
|
|
They're basically someone who's paid to be the one who gets the blame when security is found to be lax.
|
|
|
|
|
dang, I should consider myself lucky to have an actively involved CISO (first cyber job and first time working w/ a CISO). Our team is fairly small so idk if that helps.
|
|
|
|
BlankSystemDaemon posted:They're basically someone who's paid to be the one who gets the blame when security is found to be lax. Previous job had a "virtual" CISO as part of a security package we bought from the firm. Ours flat out told us that one of their services was being a glorified fall guy for when something bad eventually happened.
|
|
|
|
BlankSystemDaemon posted:They're basically someone who's paid to be the one who gets the blame when security is found to be lax. Yeah, CISOs are basically the fall guys
|
|
|
|
Our company just had a investment firm buy a controlling interest in the company. As a result they came through and had outside dudes do an audit on our infrastructure for stuff we had to do. One of their action items was "Hire/designate someone as CISO". The entire IT/Cybersec department laughed at that, which is to say the three of us laughed at that.
|
|
|
|
Unauth Vcenter RCE through vsphere client, yay! https://twitter.com/WeisterCreek/status/1364319729515716612?s=20
|
|
|
|
Defenestrategy posted:Our company just had a investment firm buy a controlling interest in the company. As a result they came through and had outside dudes do an audit on our infrastructure for stuff we had to do. One of their action items was "Hire/designate someone as CISO". You have a cybersec department? Lucky.
|
|
|
|
Cup Runneth Over posted:You have a cybersec department? Lucky. Well in so far as I am a "Infrastructure Security Engineer" and my job is to come up with policies that make everyone miserable, and then implement them.
|
|
|
|
Defenestrategy posted:Well in so far as I am a "Infrastructure Security Engineer" and my job is to come up with policies that make everyone miserable, and then implement them. Like I said, lucky. My job entails an executive telling me "we want this app to be secure" and then leaving it up to us to figure out what the best practices are and how to implement them. And we don't get paid extra for it.
|
|
|
|
Is this bad? This is bad, right?
|
|
|
|
Last Pass just keeps knocking it out of the park. https://www.theregister.com/2021/02/25/7_trackers_in_lastpass_android/
|
|
|
|
Only if HR finds out about it before your next contract renegotiation where they somehow agree to double your pay. But for real, yeah, this is potebtially bad if you work somewhere that likes to run outdated versions of Acrobat Reader or one of the vulnerable apps.
|
|
|
|
Is this the place to ask about implementing crypto? I'm converting a library that uses OpenSSL for AES-256-GCM to use CNG/BCrypt, and I'm unsure about nonce generation. The docs for the BCRYPT_AUTHENTICATED_CIPHER_MODE_INFO struct specify that a nonce needs to be present for CCM and GCM (this is a separate nonce from the IV, I think, but the OpenSSL and CryptoPP implementations don't say anything about it, or seem to equate the IV and the nonce. What is that nonce supposed to be?
|
|
|
|
Is there a reason you can't use a library that's already in place? I'm pretty sure the wide thread opinion on implementing crypto is "don't do that," as evidenced by the thread title.
|
|
|
|
CryptoAPI NG/ BCrypt _is_ the library in place. The default crypto library for windows. OP I am not qualified to answer this because I'm not a professional developer but with counter modes like CCM or GCM the nonce is very important. It has to be random and unique for each message. This is because those modes are effectively using AES as a keystream generator and XOR-ing this with the plaintext, and with stream ciphers it is very bad if the keystream is the same for two messages because you can XOR those again and recover parts of the keystream.
|
|
|
|
more falafel please posted:Is this the place to ask about implementing crypto? I'm converting a library that uses OpenSSL for AES-256-GCM to use CNG/BCrypt, and I'm unsure about nonce generation. The docs for the BCRYPT_AUTHENTICATED_CIPHER_MODE_INFO struct specify that a nonce needs to be present for CCM and GCM (this is a separate nonce from the IV, I think, but the OpenSSL and CryptoPP implementations don't say anything about it, or seem to equate the IV and the nonce. What is that nonce supposed to be? I feel like if you need to ask a question like this on an internet forum, you should not try to roll your own crypto.
|
|
|
|

|
| # ? Apr 19, 2024 03:30 |
|
more falafel please posted:Is this the place to ask about implementing crypto? I'm converting a library that uses OpenSSL for AES-256-GCM to use CNG/BCrypt, and I'm unsure about nonce generation. The docs for the BCRYPT_AUTHENTICATED_CIPHER_MODE_INFO struct specify that a nonce needs to be present for CCM and GCM (this is a separate nonce from the IV, I think, but the OpenSSL and CryptoPP implementations don't say anything about it, or seem to equate the IV and the nonce. What is that nonce supposed to be? It's been a little bit since I did this stuff but from memory the distinction between an IV and a nonce is in how each mode uses the value and the mode's requirement for how it is generated. For CBC mode the IV is used as the initial value the block cipher operates against when encrypting the first block. Because the block size is known, and the encryption process is chained, patterns between encrypted values can be deduced if the IV is known or shared between those values and the first few bytes of the plaintext are the same. Therefore, the IV must be random or pseudorandom in CBC mode. For GCM mode, the initialization value is a nonce (number used once) and must be unique, but not necessarily random or pseudorandom, for each use of the same key. Thus, the nonce can simply be a sequential value provided the party encrypting can guarantee that the value isn't reused. Using a random nonce introduces the potential for nonce collision sooner than using a sequence. The thing to remember is that CBC vs GCM is really more of a question between block encryption and stream encryption. Because GCM is a counter method the internal counter is known and a reused nonce can leak the XOR of plaintexts. If the attacker can determine one plaintext then it can decrypt others. CBC mode doesn't have that issue, although it's vulnerable to padding oracle attacks. But, the important thing here is always rtfm for crypto and never roll your own.
|
|
|
























 Cat Army
Cat Army