|
Crossposting from the infosec thread:ratbert90 posted:https://wiki.archlinux.org/index.php/SELinux Arch is so loving bad.
|
|
|
|

|
| # ? Apr 29, 2024 01:41 |
|
i put lubuntu on an i3 nuc for a plex server and it's been suiting my needs. that's my linux story hope you enjoyed it.
|
|
|
|
Endless Mike posted:i put lubuntu on an i3 nuc for a plex server and it's been suiting my needs. you have a gui on your server?
|
|
|
|
ratbert90 posted:Crossposting from the infosec thread: My main problem with Arch at the moment (and it's a big one) is that the Arch Build System has builds for debug symbol packages, they just don't publish them. So if you want debug symbols then you have to locally recompile everything, which kinda sucks. It's a big enough deal that I'm considering switching to Fedora now that GNOME 3.20 actually seems to basically work, even in Wayland mode, and I'm not forever hoping that they maybe the next release will finally be the one where they fix poo poo. As for SELinux, I really don't know what to think about it. It seems rather quaint these days, and I feel like you can just assume that your kernel is compromised the moment an attacker gets local code execution, what with there being so many local root holes. Is this actually the case? I genuinely don't know. My instinct is to say that you should compartmentalize your services using virtualization, because virtio PCI devices have a much narrower attack surface than all the myriad syscalls and api filesystems of a typical modern Linux kernel.
|
|
|
|
Mr Dog posted:As for SELinux, I really don't know what to think about it. It seems rather quaint these days, and I feel like you can just assume that your kernel is compromised the moment an attacker gets local code execution, what with there being so many local root holes. Is this actually the case? I genuinely don't know. My instinct is to say that you should compartmentalize your services using virtualization, because virtio PCI devices have a much narrower attack surface than all the myriad syscalls and api filesystems of a typical modern Linux kernel. Source your quotes
|
|
|
|
Mr Dog posted:My main problem with Arch at the moment (and it's a big one) is that the Arch Build System has builds for debug symbol packages, they just don't publish them. So if you want debug symbols then you have to locally recompile everything, which kinda sucks. It's a big enough deal that I'm considering switching to Fedora now that GNOME 3.20 actually seems to basically work, even in Wayland mode, and I'm not forever hoping that they maybe the next release will finally be the one where they fix poo poo. Kernel memory space is clearly defined and is absolutely NOT compromised immediately when an attacker gets local code execution.
|
|
|
|
If you get owned in kernel mode then SELinux isn't going to do a loving thing to mitigate damage. If you're confident that not a single syscall or api filesystem running on your machine can be exploited to get unconfined root then sure, SELinux makes for great damage control. If you believe in defence in depth then maybe you'll be a bit more skeptical. And you believe that the actual public CVE and patch will go out before the botnet does, which is probably a safe assumption but who knows these days. From where I stand Torvalds has a very cavalier attitude towards security bugs, as evidenced by the fact that the grsecurity kernel patch set exists and isn't getting merged any time soon. So there's your source. Enjoy getting wrecked by the next local privilege escalation CVE I guess?
|
|
|
|
so whats the easiest way for me to do installation over a network interface then? i have an ethernet adapter for this thing so i am open to suggestions
|
|
|
|
ratbert90 posted:Crossposting from the infosec thread: hahahahha
|
|
|
|
Mr Dog posted:I don't know how selinux works
|
|
|
|
b0red posted:you have a gui on your server? I wanted it for setup. not so necessary now.
|
|
|
|
Mr Dog posted:If you get owned in kernel mode then SELinux isn't going to do a loving thing to mitigate damage. Also SELinux helps quite a bit because a RCE can be prevented via SELinux contexts in a lot of cases (hence mitigation.) quote:If you're confident that not a single syscall or api filesystem running on your machine can be exploited to get unconfined root I'm not; hence why I use SELinux, along with Red Hat and the NSA. It sounds to me like you have a fundamental misunderstanding of how SELinux works/What SELinux is. quote:
quote:And you believe that the actual public CVE and patch will go out before the botnet does, which is probably a safe assumption but who knows these days. That's why you have damage mitigation control Jesus Christ stop talking and go open a book, or hell, talk to the selinux devs on freenode. quote:From where I stand Torvalds has a very cavalier attitude towards security bugs, as evidenced by the fact that the grsecurity kernel patch set exists and isn't getting merged any time soon. Grsecurity refuses to work with Linus. "Hey guys let's submit a gigantic blob of code and then bitch on the mailing list when it isn't accepted" is a great way of doing business. quote:So there's your source. Enjoy getting wrecked by the next local privilege escalation CVE I guess? I won't, because I stay up to date and keep SELinux set to enforcing. Alternatively this: jre posted:
FlapYoJacks fucked around with this message at 23:20 on Jul 13, 2016 |
|
|
|
i got the 2004 o'reilly selinux book for a penny on amazon. doubt its 100% relevant still but gonna thumb through it anyway
|
|
|
|
b0red posted:i got the 2004 o'reilly selinux book for a penny on amazon. doubt its 100% relevant still but gonna thumb through it anyway A great first tutorial is: https://www.youtube.com/watch?v=cNoVgDqqJmM&hd=1
|
|
|
|
ratbert90 posted:A great first tutorial is: 10/10 have watched and taken notes a bit ago
|
|
|
|
Endless Mike posted:I wanted it for setup. not so necessary now. Edit your /etc/inittab and change that bitch to runlevel 3.
|
|
|
|
Mr Dog posted:i dont know how selinux or kernel development works and all my arguments are bizarro cargo culting that even anti-systemd fanatics would find a bit much ran this post through the translator and it makes much more sense
|
|
|
|
b0red posted:i got the 2004 o'reilly selinux book for a penny on amazon. doubt its 100% relevant still but gonna thumb through it anyway for a lot of the fundamentals, it is still surprisingly relevant, and it's interesting to thumb through to see how it evolved keep in mind that the biggest change between then and now is the introduction of targeted policy. This means that servers and services, which come with selinux policies, have selinux policies enforced against them. A normal admin running a shell as root has no restrictions and can do whatever.
|
|
|
|
trilljester posted:Edit your /etc/inittab and change that bitch to runlevel 3. code:celeron 300a posted:for a lot of the fundamentals, it is still surprisingly relevant, and it's interesting to thumb through to see how it evolved Will probably give it a better read then when I get some time. Cheers
|
|
|
|
I don't know how selinux works internally. can anyone answer how it mitigates a privesc bugs?
|
|
|
|
Shinku ABOOKEN posted:I don't know how selinux works internally. can anyone answer how it mitigates a privesc bugs? first off, if you can't make the call that contains the bug, you can't exploit kernel bugs. on the userspace side, even if you manage to get yourself to be uid=0, you still can't do anything that selinux doesn't allow you to do. ok so great you compromised my apache daemon and you now have root inside of apache's selinux context. have fun reading the apache directories and writing to sockets bound to port 80, because those are the only things selinux will permit you to do.
|
|
|
|
Mr Dog posted:If you get owned in kernel mode then SELinux isn't going to do a loving thing to mitigate damage. If you're confident that not a single syscall or api filesystem running on your machine can be exploited to get unconfined root then sure, SELinux makes for great damage control. the real question is, can an attacker make those buggy syscalls or touch esoteric filesystems? i mean, yeah, if the attacker is a legitimate user and has a login shell in an unconstrained selinux context, selinux isn't going to help you. if he hacked his way in via a vulnerability in some network service, the attacker is very tightly constrained, and it's extremely unlikely he's going to find a second or third vulnerability to break out of his selinux context.
|
|
|
|
Notorious b.s.d. posted:ok so great you compromised my apache daemon and you now have root inside of apache's selinux context. have fun reading the apache directories and writing to sockets bound to port 80, because those are the only things selinux will permit you to do. i'm the security-conscious sysadmin who is using mandatory access controls at the kernel level to block tls connections to his web server
|
|
|
|
cadenza posted:so whats the easiest way for me to do installation over a network interface then? i have an ethernet adapter for this thing so i am open to suggestions if it was a normal workstation you'd just set up a tftp server on the same subnet, boot to the PROM monitor, set a local IP, and then boot straight from a kernel on the tftp server
|
|
|
|
cadenza posted:so whats the easiest way for me to do installation over a network interface then? i have an ethernet adapter for this thing so i am open to suggestions pxe boot is not for the light hearted your bios needs to support pxe booting or you will need some other way to do a network boot you need to be able to configure and run an isc dhcp server on the ethernet segment that your laptop will be on, which means you will need a spare computer and put everything on a new ethernet segment or turn off whatever dhcp server is already running. you will need to add tftp support and either http or nfs support to the spare computer. you probably want to install wireshark or tcpdump to debug any issues if you wish to walk down this path, see if there is a distribution with up to date instructions (maybe arch?) or a blog post. I can try to make some fedora 24 specific instructions but not anytime soon. celeron 300a fucked around with this message at 08:42 on Jul 14, 2016 |
|
|
|
celeron 300a posted:pxe boot is not for the light hearted just plug computer 1 directly into computer 2. you have to do all this crap for half the embedded boards out there, its not that big of a hassle by linux standards
|
|
|
|
hobbesmaster posted:just plug computer 1 directly into computer 2. you have to do all this crap for half the embedded boards out there, its not that big of a hassle by linux standards this can be part of a good solution but remember to turn on ip masquerading if your install target needs internet
|
|
|
|
SERIOUSLY THOUGH If you are getting squashfs errors, see if you can switch to a different terminal with kernel log output (alt-f2 or ctrl-alt-f2, repeat for other function keys until you see something) to see if you are getting read errors so that you can single out your usb drive (or usb port or usb bus) as being bad. Or it might be able to finger another culprit. If it is not a drive read error then you could have bad memory, a bad bus, a bad heatsink fan, a bad processor, or a misconfigured (or unconfigured) device that is behaving unusually bad. If you have a brand new laptop, it might be worth waiting until the next release of your chosen distro in case newer drivers help.
|
|
|
|
what is with all the 'not a valid com32r image' errors i've been encountering lately
|
|
|
|
celeron 300a posted:SERIOUSLY THOUGH thanks for the reply friend i did a memory test and it was fine. the usb drives all work fine on other machines. they also all work fine if i'm just using them as FAT storage media - if i plug a USB drive into either of the ports on the machine and mount it i have no problems, its literally only when reading the compressed filesystem from installation media that presents problems. the images i've tried (all 4 of them) all have the right md5 checksums too, so its not a problem with my source images. i would have assumed its just some weird idiosyncrasy of the machine (new thinkpad x1 carbon) but no-one else online seems to be experiencing this, which points towards some hardware problem rather than anything else. are there some magic usb boot settings i might be missing from the bios? that would be nice rather than having to try sending it back to lenovo...
|
|
|
|
Captain Foo posted:what is with all the 'not a valid com32r image' errors i've been encountering lately insufficient communism. stab your boss
|
|
|
|
celeron 300a posted:pxe boot is not for the light hearted uefi made this even worse it's all the challenges of pxe booting but with the added joy that often it doesn't work, because uefi firmwares are still buggy as poo poo
|
|
|
|
celeron 300a posted:pxe boot is not for the light hearted I haven't encountered a computer in the last 10 years that didn't support pxe boot
|
|
|
|
coincidentally, nobody has used pxe boot in the last 10 years
|
|
|
|
atomicthumbs posted:coincidentally, nobody has used pxe boot in the last 10 years pxe boot is used pretty much universally
|
|
|
|
atomicthumbs posted:coincidentally, nobody has used pxe boot in the last 10 years the exception to every "nobody has used _____ in the last 10 years" is always embedded except irda. nobody has ever seen irda work
|
|
|
|
atomicthumbs posted:coincidentally, nobody has used pxe boot in the last 10 years it's a great way for windows computer touchers to image laptops imo. my first part time gig in high school i set one up with the one lady shop, was kinda of cool and definitely makes life easier. had the ability to boot a few linux rescue discs with it as well
|
|
|
|
Pxe boot + anaconda kickstart file == rapid deployment of RHEL servers.
|
|
|
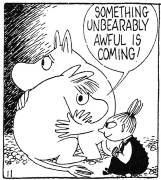
ratbert90 posted:Pxe boot + anaconda kickstart file == rapid deployment of RHEL servers.
|
|
|
|
|

|
| # ? Apr 29, 2024 01:41 |
|
ok let me rephrase that. nobody who's not a fuckin nerd has used it in the last 10 years
|
|
|