|
mystes posted:How about this except rather than a kernel parameter we just make another version of /dev/urandom that blocks so programs can choose which one they want to read from? We can call it /dev/urandom2 or something. Whoa, you're starting to make too much sense here. We need to get every user compiling a kernel themselves, otherwise how will they learn!
|
|
|
|

|
| # ? Apr 28, 2024 10:49 |
|
clearly seeding the prng is not something the kernel should be doing, since it doesn�t know what the numbers are going to be used for. instead we should have a generic interface of the form /dev/prng/$seed, and leave it up to userspace callers to choose a seed with an appropriate level of entropy for their use case.
|
|
|
|
the kernel should be deterministic, why do we even have rng involved it just breaks the test cases
|
|
|
|
https://twitter.com/TinkerSec/status/1174749392382976003?s=09
|
|
|
|
just have the user decide how random they want something to be by flipping coins themselves and if they want secure randomness then do the flipping securely
|
|
|
|
A proper rng could generate the exact same data as a prng. who cares.
|
|
|
|
Honestly, if they want to have some sort of insane battle between levels of government that's fine, but lol at the pen testers being dragged into it.
|
|
|
|
Well at least there is no mandatory minimum on burglaries. quote:Third Degree Burglary charged as a Class D felony is punishable by a maximum of 5 years imprisonment and a fine up to $7,500.
|
|
|
|
Progressive JPEG posted:just have the user decide how random they want something to be by flipping coins themselves and if they want secure randomness then do the flipping securely just lol if u dont hire a NFL Referee to do your coin tosses flipping your own coins is anti union
|
|
|
|
Media Bloodbath posted:Well at least there is no mandatory minimum on burglaries.
|
|
|
|
Media Bloodbath posted:Well at least there is no mandatory minimum on burglaries. you still end up with a felony that will haunt you for the rest of your life even if it�s knocked down to a misdemeanor these guys will still have an arrest record which can come up at inopportune times
|
|
|
|
if all else fails this would be a great place for a pardon
|
|
|
|
haveblue posted:if all else fails this would be a great place for a pardon by whom? trump would prolly want to see the security folks executed, not pardoned, the Police and state authority should be the only ones with access to things! Hackers are evil and should be punished etc etc etc
|
|
|
|
the state governor. president can't pardon county/state crimes anyway
|
|
|
|
Farmer Crack-rear end posted:the state governor. president can't pardon county/state crimes anyway Who is a republican so exact same difference? right-wing authority does not want hackers to exist
|
|
|
|
this is indiana, i'm sure the state-level officials who started doing these security checks are also republicans
|
|
|
|
rjmccall posted:this is indiana, i'm sure the state-level officials who started doing these security checks are also republicans iowa, and yeah that doesnt matter anymore. The problem is they got hacked and need to punish the hackers. Simple as that.
|
|
|
|
Sniep posted:The problem is they looked dumb and need to punish the people who made them look dumb. Simple as that.
|
|
|
|
Secfuck New client: the login process continues to be distracting, I'm probably spending 20mins a day waiting to get back into my notes. How are we going with room based logins? I think we need to extend the logout delay and just close the computer from PROGRAM using KEYCOMBO like we used to, this allows almost instant access. KEYCOMBO in question just locks the medical application, If you cancel it you get taken back to a normal desktop, PROGRAM logins are weak using short staff codes. Previous IT company has 12 hour screen locks and generic desktop logins with password=username. When they came to us they go individual logins and 15min screen locks. It's taken C-level intervention and showing them govt standards and still some doctor's are complaing there's no issue with the old way
|
|
|
|
ya, that. but publically, it's being Strong Against Cyber Crime
|
|
|
|
While i hope otherwise of course, I have a bad feeling about those pentesters. I'd not be surprised if they got 20 years type poo poo, examples made of
|
|
|
|
Progressive JPEG posted:just have the user decide how random they want something to be by flipping coins themselves and if they want secure randomness then do the flipping securely please jiggle mouse to continue booting
|
|
|
|
Sniep posted:iowa, and yeah that doesnt matter anymore. thats not what happened, its a pissing match between the local sheriff and the state government
|
|
|
|
duz posted:thats not what happened, its a pissing match between the local sheriff and the state government my point was that depending on which way the wind blows, that piss stream could end up loving them. i just don't envy their position, especially when caught up in that specific political flavor of pissing match i hope the case gets dropped but WHO KNOWS in this wild world lately
|
|
|
|
the pentesters obviously weren't very good if they got caught anyway
|
|
|
|
Methanar posted:the pentesters obviously weren't very good if they got caught anyway 
|
|
|
|
su /san/sarandon
|
|
|
|
quote:Bisignano said it's important to test the safety of government systems. He believes a test of vulnerability could have been accomplished in a less covert way than a "CIA-type action." They deserve to be broken into
|
|
|
|
Politician and Legal doesn't understand tech or security, news at 11.
|
|
|
|
up next, a champion boxer who went his whole life without ever being punched by a sparring partner
|
|
|
|
CommieGIR posted:Its looks like the Iowa Pen Test gig, they were authorized to be there, they showed the Sheriff their documentation, and he arrested and charged them anyways. This is some straight-up color-of-law malicious prosecution poo poo right here.
|
|
|
|
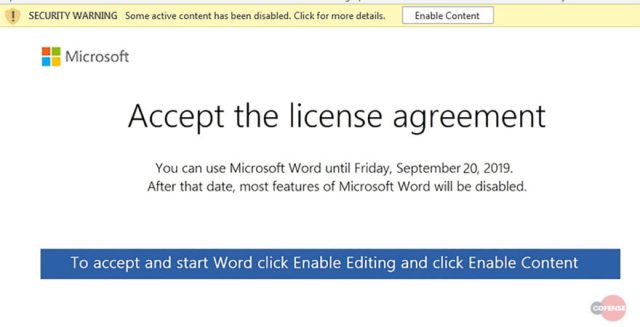 possibly the world's most effective malware scheme there is basically no way to inoculate users against opening documents from someone they trust, doubly so as part of an ongoing conversation.
|
|
|
|
infernal machines posted:
finding old email threads and quote-replying to them with attachments seems like an obvious, great idea, i wonder why literally every piece of malware doesn't do that
|
|
|
|
Shame Boy posted:finding old email threads and quote-replying to them with attachments seems like an obvious, great idea, i wonder why literally every piece of malware doesn't do that
|
|
|
|
loving lamo. @erratarob is an rear end in a top hat but goddamn he can gently caress up snake oil salesmen https://twitter.com/ErrataRob/status/1175045949367967746?s=20
|
|
|
|
ewiley posted:loving lamo. @erratarob is an rear end in a top hat but goddamn he can gently caress up snake oil salesmen 256 and 512 RSA have been crackable for a while. Which is why even 1024 is deprecated. 2048 or higher or bust. I want to say they are recommending a minimum of 2048 to be secure till 2030 and 3072 if you want assurances beyond that. From Wikipedia, and a little dated: NSA Recommended Algorithm Usage RSA 3072-bit or larger Key Establishment, Digital Signature Diffie-Hellman (DH) 3072-bit or larger Key Establishment ECDH with NIST P-384 Key Establishment ECDSA with NIST P-384 Digital Signature SHA-384 Integrity AES-256 Confidentiality CommieGIR fucked around with this message at 16:04 on Sep 20, 2019 |
|
|
|
CommieGIR posted:256 and 512 RSA have been crackable for a while. Which is why even 1024 is deprecated. 2048 or higher or bust. I want to say they are recommending a minimum of 2048 to be secure till 2030 and 3072 if you want assurances beyond that. Anything above RSA 2048 is a waste of time since asymmetric keysize is irrelevant in a post-quantum world. Just use 2048 and wait till the post-quantum algorithms come out and switch to those. Using a classical computer to break RSA would be interesting, but it's basically dead-algorithm-walking as it is. Symmetric (for now) just use AES 256 e: the NSA abandoned Suite-B for this very reason https://en.wikipedia.org/wiki/NSA_Suite_B_Cryptography ewiley fucked around with this message at 16:04 on Sep 20, 2019 |
|
|
|
ewiley posted:Anything above RSA 2048 is a waste of time since asymmetric keysize is irrelevant in a post-quantum world. Just use 2048 and wait till the post-quantum algorithms come out and switch to those. Using a classical computer to break RSA would be interesting, but it's basically dead-algorithm-walking as it is. Agreed, just saying that's what I've seen recommended. Yeah, CNSA is the current standard.
|
|
|
|
okay but how does factoring 256-bit RSA tie into their infinite prime number prediction pattern breakthrough? are they attending 36c3? e: who uses 3072?
|
|
|
|

|
| # ? Apr 28, 2024 10:49 |
|
I use 3073, because it's twice as good
|
|
|